Featured Content
Book
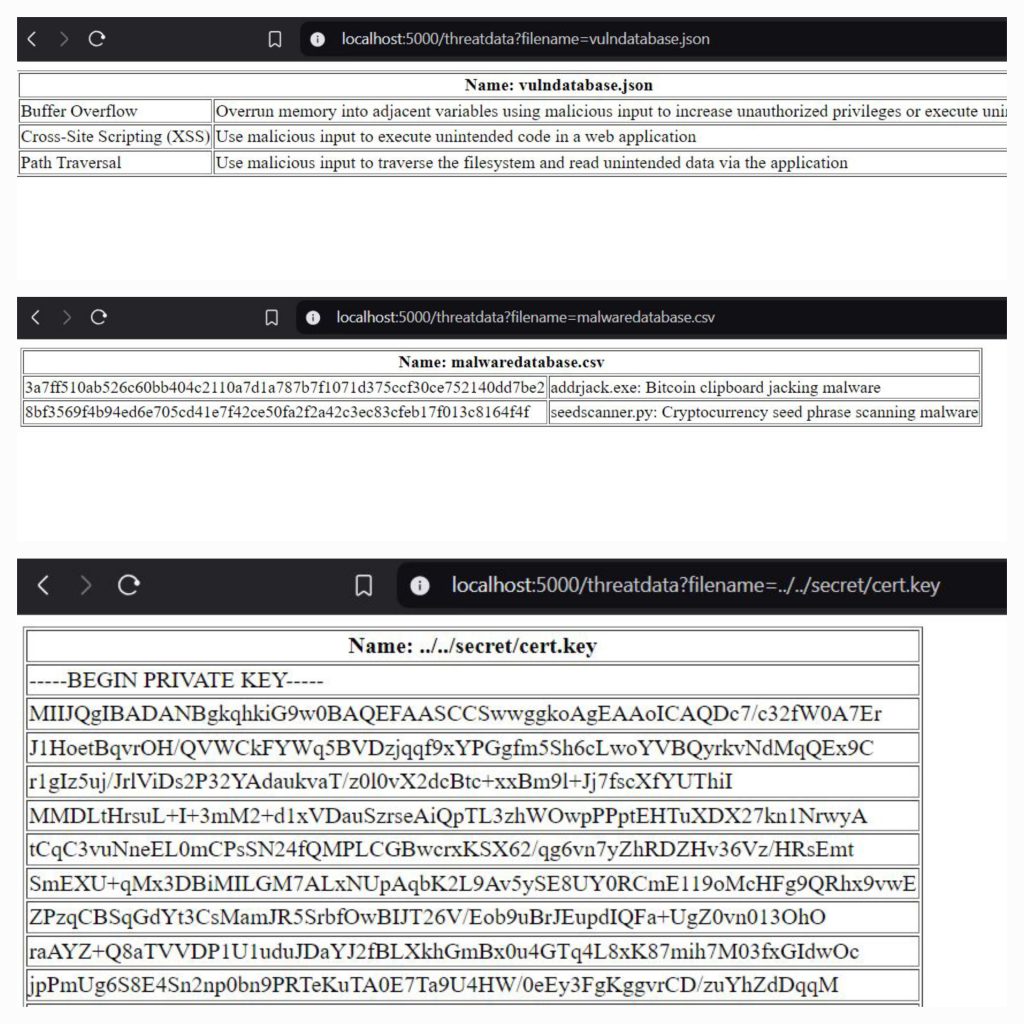
Digital Sovereignty: Protecting Your Crypto Assets Against Common Threats
EBook: https://www.amazon.com/dp/B0F3WJ6MTJ
EBook (B&N): https://www.barnesandnoble.com/w/digital-sovereignty-josh-mcintyre/1147312993?ean=2940182032216
EBook (additional retailers): https://books2read.com/digitalsovereignty
Paperback: https://www.amazon.com/dp/B0F47FMHPK
Paperback (B&N): https://www.barnesandnoble.com/w/digital-sovereignty-josh-mcintyre/1147312993
Direct USD or Crypto (EBook & Paperback): https://chaintuts.store
Open Source Repo (Individual Chapters): https://github.com/chaintuts/crypto-book
Latest Video Tutorials
Latest Article Tutorials
https://github.com/chaintuts/articles/tree/development/pdf
Latest Slides
https://github.com/chaintuts/slides/tree/development/pdf
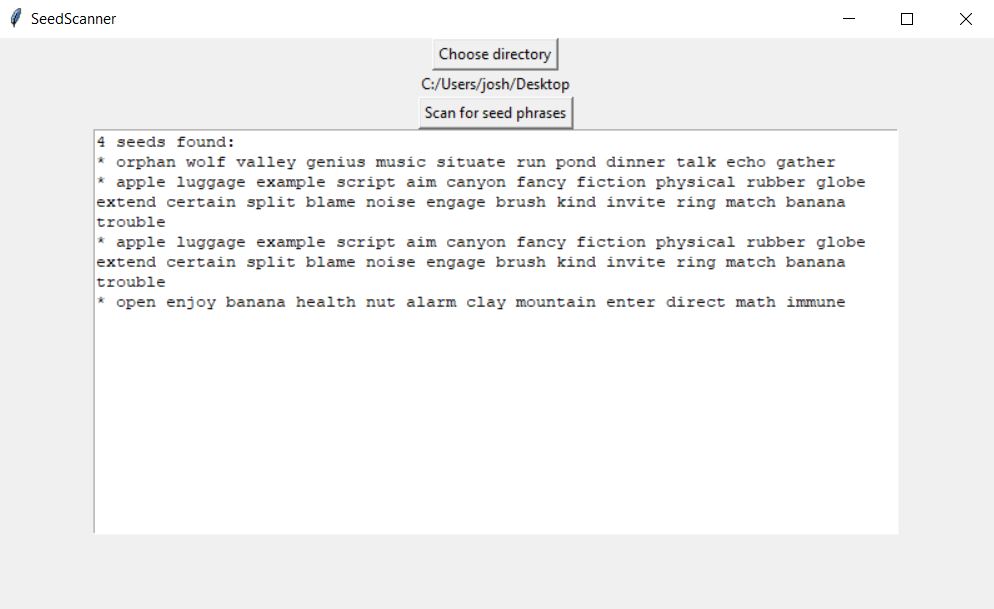
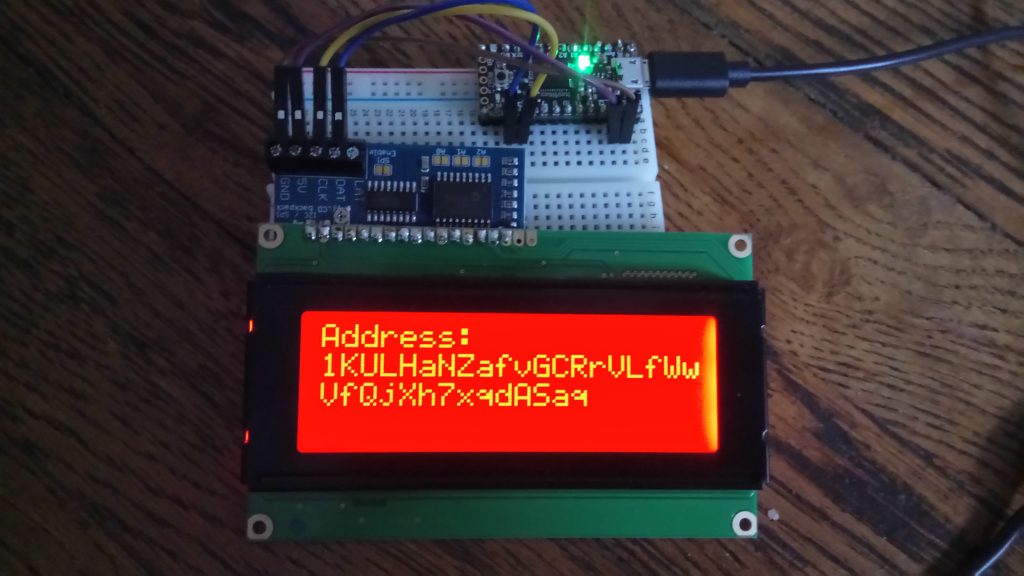
Latest Code